Text by CLOT Magazine
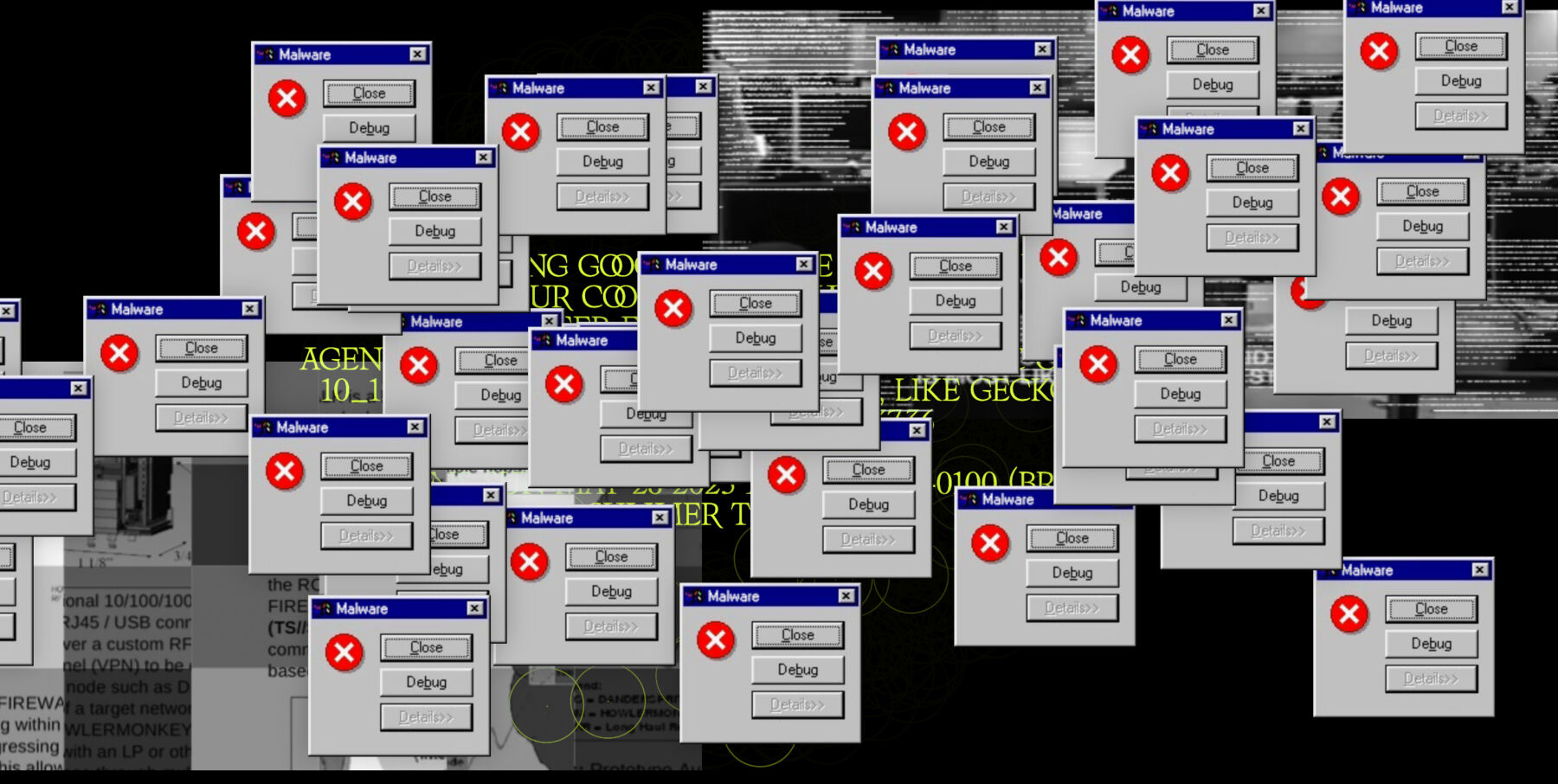
33 years ago, the first digital virus was created. Ever since millions of viruses have been designed, billions of devices fallen prey to them, and billions of pounds wasted in damages. What was meant to be a harmless prank soon turned into a geopolitical weapon able to steal private information, disrupt economies, and threaten governments? And yet, in a bizarre way, there is a beauty and sophistication in the elegant design and catastrophic consequences of viruses. Malware: Symptoms of Viral Infection, which opens from July 4 to November 9, 2019, in Het Nieuwe Instituut, Rotterdam, explores this duality.
The exhibition, curated by Bas van de Poel and Marina Otero Verzier, delves into the history of viruses from their innocent conception to their transformation into the tools of global cybercrime, highlighting the infamous cases. It begins with the comparatively inoffensive DOS viruses used by software engineers to investigate the capabilities of operating systems. Using simulation software, historical data, and artistic representation, the exhibition explores the concepts of digital safety, surveillance, and cyberwarfare in the age of technological boom.
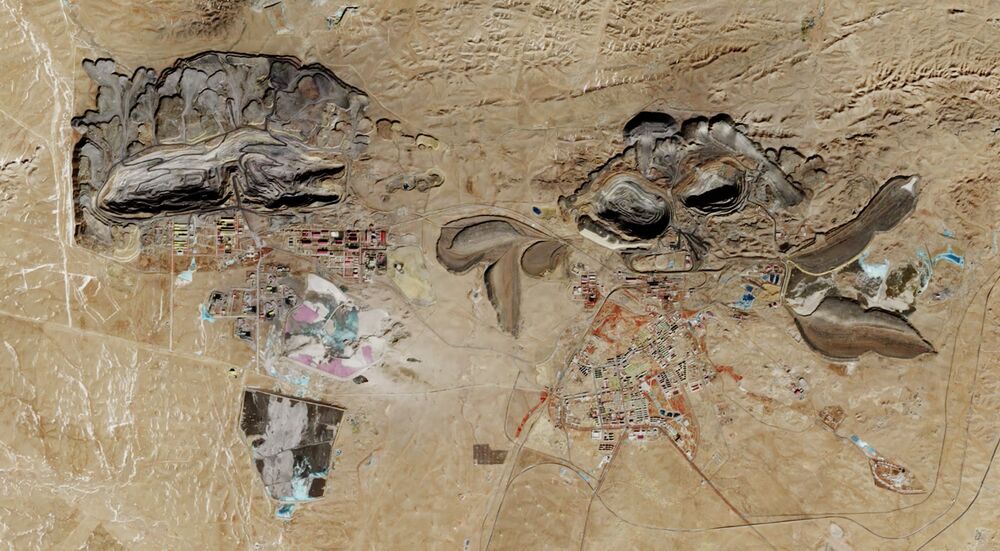
Nowadays, as we become more dependent on technology and automation, infrastructures like energy, water, transport, financial and social services are at a high risk of being corrupted by viruses. The wide reach of the internet makes it exponentially harder to prevent their spreading, while the progress in AI and machine learning creates smarter viruses able to mimic and manipulate people’s behaviour, leading to more targeted and destructive cyber attacks.
As these attacks grow increasingly elaborate, threatening national borders and interfering with international relations, governments and independent bodies have tackled down on them, employing the tricks used by the hackers and incorporating cyber measures with traditional military forces which ultimately results in cyberwars.
The ongoing controversies about confidentiality regarding information technology are closely linked to the security and surveillance structures put in place by state and intelligence agencies to combat cyber attacks and ensure public safety. Yet the same systems, along with social networking platforms, are also used by authorities and corporations to spy, gather user information, manipulate, and capitalise on people. The resulting seemingly unsolvable dilemma looms over technology designers: how do you develop effective security systems without compromising privacy in the modern day?